Threat of Employee Betrayal: Who Stands Vulnerable to the Misappropriation of Classified National Tech
In the ever-evolving landscape of innovation, distributed national innovation networks—consortia, public-private partnerships, and multi-institutional research projects—increase exposure to corporate espionage. This is due to shared resources, decentralized control, high-value targets, and supply chain vulnerabilities.
Small businesses and universities, in particular, may hold valuable, niche intellectual property but lack robust security infrastructure, making them attractive targets for corporate espionage. To combat this, experts recommend a multi-faceted approach.
1. **Comprehensive Risk Assessment**: Identify assets, assess threats, and conduct vulnerability analysis to understand potential risks and prioritise protection measures.
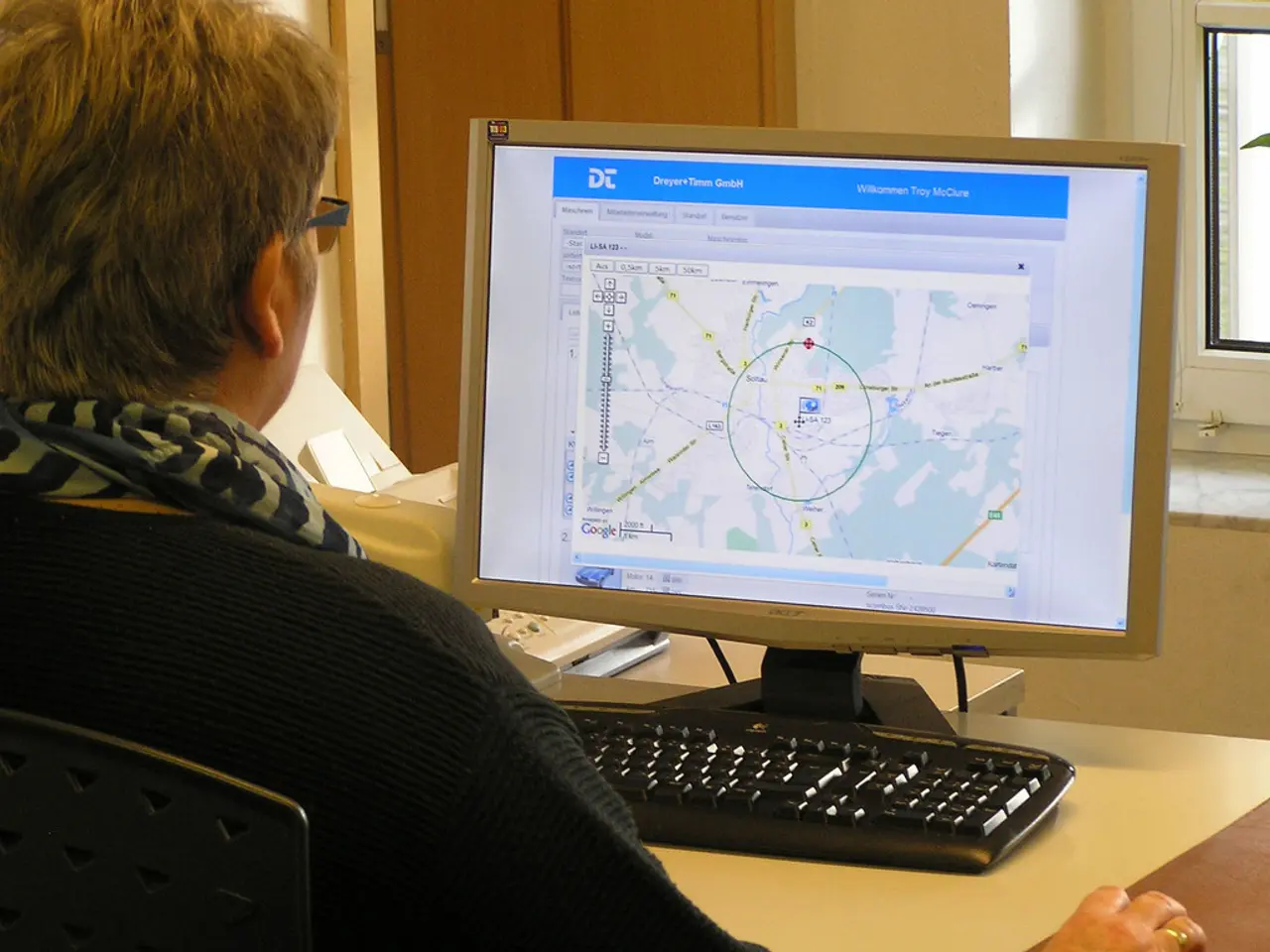
2. **Implement Layered Security**: Use encryption, multi-factor authentication, and regular penetration testing to bolster cybersecurity. Secure labs, offices, and devices, control access to sensitive areas, and limit knowledge of proprietary information on a need-to-know basis.
3. **Collaboration Protocols**: Ensure all partners sign robust Non-Disclosure Agreements (NDAs), share only what’s necessary for collaboration, and keep core intellectual property compartmentalised. Have clear procedures for reporting and responding to suspected breaches.
4. **Education & Awareness**: Regularly train employees and partners on spotting phishing, social engineering, and other espionage tactics. Foster an organisational ethos where security is everyone’s responsibility.
5. **Leverage Government & Industry Resources**: Adopt standards like NIST CSF or ISO 27001. Tap into government programs offering threat intelligence and protection resources for critical sectors.
6. **Insider Threat Programs**: Screen employees and partners, especially those with access to sensitive data, and monitor for unusual data access or transfer patterns.
For small businesses and universities, it’s crucial to invest in baseline protections, collaborate wisely, and stay current with evolving threats. Don’t assume that being small means you’re not a target—corporate espionage often targets overlooked players in innovation networks.
Despite not having direct access to specific interviews with John Doyon and Michael Crouse discussing corporate espionage in distributed national innovation networks, the above strategies reflect expert consensus on mitigating such threats. If you have direct quotes or references from these interviews, please share them, and I’ll gladly tailor my response to their specific insights.
In conclusion, vigilance, education, layered security, and smart collaboration are the watchwords for small businesses and universities in innovation networks facing corporate espionage threats. This platform, associated with The Federal Drive, offers expert content related to current events in the federal community and reserves all rights for its usage.
- To protect the federal workforce and small-business sectors within distributed national innovation networks, it's essential to promote education and awareness about the risks and tactics of corporate espionage.
- Supporting small businesses and universities in strengthening their cybersecurity infrastructure, via comprehensive risk assessments and the implementation of layered security, can help defend against potential corporate espionage.